Update
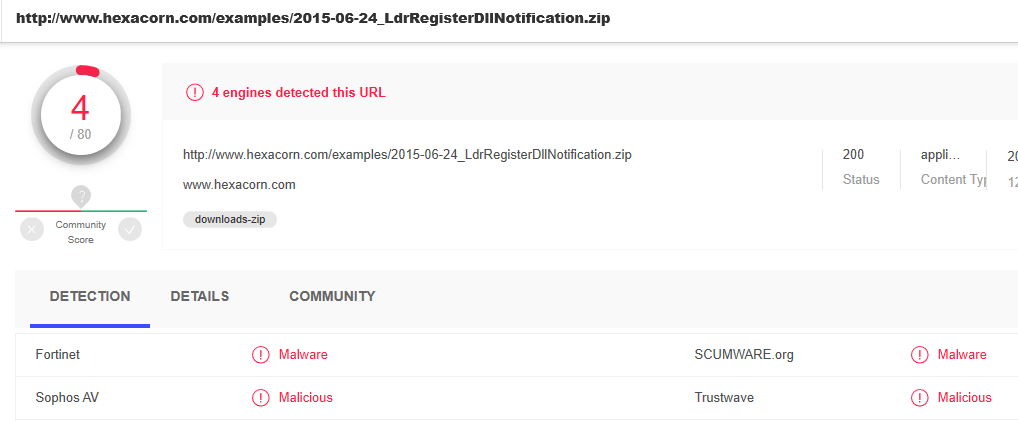
After pinging CRDF via email I got more detailed reply. Turns out their engine added my domain because of the VirusTotal report that highlights 4 detections of a POC file for LdrRegisterDllNotification API I posted in 2015.
Thank you to CRDF for engaging with me and despite our difference leading this to closure.
I have updated my pooplist accordingly, and after removing CRDF I have added the following guys:
- Fortinet
- Sophos
- Scumware.org
- Trustwave
Finally, need to reiterate that VirusTotal approach towards False Positives is absolutely disgraceful. At the very least they should offer owners of websites/software to follow up with vendors directly from the VirusTotal interface. After all, this is where these damaging detections are presented.
Update
CRDF came back to me on Twitter and we had a battle of wits. I was inclined to understand why the domain was added in a first place to which I have not received any explanation so far. VirusTotal didn’t come back at all.
Update
I submitted the URL to CRDF Labs and now it came back as FP. They say it may take 4 hours to propagate the info. I asked them why it was marked in a first place; no reply yet.
Old post
Yesterday I checked my web site on VirusTotal.

To my surprise there was one detection — I wrote about this on Twitter, and asked VirusTotal to address it. I had no idea what CRDF is at that moment, because VT doesn’t provide any immediate pointers on their report. Later on I googled around and discovered that CRDF is a French web site offering some sort of threat feeds. Today morning I checked what they have to say about my web site and this is what they state:

What the heck?
Where is the evidence to support this claim?
And it is like this for a year?
VT uses CRDF, and CRDF says that about 1 year ago my web site entered their malicious web site repo. This implies that whoever checked my web site on VT during last year, either directly (via their UI), or indirectly (API/3rd party vendor) would be warned that my site is a risk. This may sound trivial, because this is one single detection, but we live in an environment where VT feed is omnipresent. Tones of software solutions leverage VT as a part of their detection/prevention model.
Do I make this stuff up?
Have a look at this…

What happens here? A staff member of MalwareBytes shows how they approach classification. To support their b/s they reframe the discussion making it sound like a lack of TLS certificate is a justification to classify the site as bad. Moreso, they provide a link to VT and guess what… there is one detection.
This is not security. This is irresponsibility. I may sound like I am sitting on a high horse, but I used this situation to highlight how stupid the whole security detection methodology became.
And how do you classify web sites? Yes, community score is a great indicator. But… who vets that? Talking about you, Sdrickert01 (user on VT that gave a score of -1).
VT, MalwareBytes, Fortinet, Sophos, Scumware.org, Trustwave – welcome to my poop list.
And to add some positive bit… the list below shows vendors that quickly engaged and addressed my concerns:
- CRDF