When you call WinHttpOpen API you can specify the user agent that will be used in subsequent WinHTTP calls.
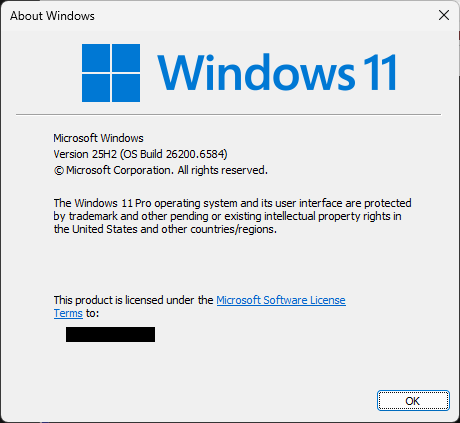
Windows OS and its native binaries use WinHttp APIs a lot, so the below is list of all user agents I could find that are used internally by Windows 11:
- Activation UX Library
- App Virt Client/1.0
- CHttpConnector
- client connection
- Client NCA
- CloudSdb
- DAFUPnP
- DavClnt
- Delegated Service Installer
- DiagnosticCSP upload
- ENROLLClient
- Escl Scan Client
- Facilitator
- FDSSDP
- HttpWrapper
- Internet Print Provider
- kerberos/1.0
- LFSVC
- MAPS_PROXY_RESOLUTION
- Microsoft BITS/7.8
- Microsoft Connection Manager
- Microsoft HP Printer Wifi Provisioning
- Microsoft NCSI
- Microsoft NetworkListManager
- Microsoft WinRM Client
- Microsoft WinRM Client – Proxy Autodetection
- Microsoft-CryptoAPI/10.0
- Microsoft-Delivery-Optimization/10.1
- MMP-C Discovery Client
- Mozilla/4.0 (compatible; MSIE 5.01; Windows NT 5.0)
- Mozilla/4.0 (compatible; Win32; NDES client 10.0.26100.4768/ge_release_svc_prod3)
- Mozilla/4.0 (compatible; Win32; NDES client 10.0.26100.5074/ge_release_svc_prod3)
- Mpssvc Proxy Detection
- MSAWindows/55
- msde/10.0
- MSDW
- MSPROV
- MSRPC
- MS_WorkFoldersClient
- NetworkProxyCSP
- OneSettingsQuery
- OTPCEP Client
- Peernet HTTP Transport/1.0
- ProxyResolver/1.0
- PushButtonReset
- rasapi32
- RPCPing
- SLSSoapClient
- SSTP
- TenantRestrictions
- TSG connection
- TSWorkspace/2.0
- TSWorkspace/3.0
- User-Agent: Microsoft-DLNA DLNADOC/1.50
- WebDefenseClient
- WicaAgent
- Windows Credential Recovery Client
- Windows Device Management Platform
- Windows Dlp Manager
- Windows EK Retrieval 1.0
- Windows Health Cert Retrieval 1.0
- Windows LAPS
- Windows Print User Agent
- Windows Store/1.0
- Windows Web Sign-in Client
- Windows-AzureAD-Authentication-Provider/1.0
- WinHTTP connection from WS to IMDS
- WinHTTP global session
- WinHTTP Session
- WinHttpGetIEProxyConfigForCurrentUser Redirect
- WSDAPI
- XblAuthManager