In one of the older posts, I talked about how the Prefetch file names are created. Today I was looking at program execution from network shares i.e. originating from the UNC paths and realized that I have not included these in the original article.
VM Shares
To test what happens, I launched WinXP under windbg and put a breakpoint on the hashing function and then executed a test file from a shared VM folder – the screenshot shows the mapping between the drive and the UNC path where the executable is placed:
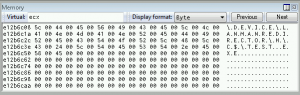
Once executed, the windbg popped up and I could trace the full path to a file in a Memory window
 As it seems, nothing really surprising:
As it seems, nothing really surprising:
- z:\test.exe is executed
- it is mapped to its UNC path \\vmware-host\Shared Folders\X\test.exe
- which is then prepended with a device name responsible for HGFS file system (used internally by VM) to form a final string used in a hash calculation
- \DEVICE\HGFS\VMWARE-HOST\SHARED FOLDERS\X\TEST.EXE
Real share
Now, that was the case with a ‘fake’ share created by the VM software.
What about a real share?
Following the same procedure:
- I mapped a host \\H\C$ drive as N: inside the guest system with ‘net use’
- and then executed N:\test.exe
The result shown below is not very surprising either as now the path refers to LANMANREDIRECTOR:
- \DEVICE\LANMANREDIRECTOR\H\C$\TEST.EXE
Substed paths
And in case you are curious what happens to drives created with subst…
For drives mapped locally using ‘subst drive: path’ e.g.
subst g: .
there is no difference as the device will refer to HARDDISKVOLUME### (where ### is hard drive’s number) – I don’t include screenshot here as I hope this example doesn’t need one.
However, using subst in a slightly different way i.e. referring to target path via localhost’s IP: e.g.
subst g: \\127.0.0.1\c$
will make the Prefetch file name to be created using the following path:
- \DEVICE\LANMANREDIRECTOR\127.0.0.1\C$\TEST.EXE
As you can see, each of the test files created a different hash
In other words, there is plenty of ways to abuse the file naming creation of the prefetch file and it’s quite hard to write an universal hash calculator to cover all these cases – it really depends on the environment and there are lots of tricks to confuse the system + I bet there are a few more that wait to be uncovered.