Testing, testing, testing… such an important part of the software development cycle. So important that its components are often referenced in the release code.
The testing functionality in Microsoft products is nothing new. I wrote about it here, and here. And today I will write about yet another component which appears to be testing-related and… can be abused to achieve persistence. This time, on Windows 10 only (have not tested servers).
When Windows 10 accepts the remote desktop session, it queries the following Registry key:
- HKLM\SYSTEM\CurrentControlSet\Control\
Terminal Server\AddIns\TestDVCPlugin
If such key exists, the OS will attempt to read the Path value underneath.
Once the Path is read, the DLL that it points to will be loaded via LoadLibrary.
And that’s it! We now have yet another persistent mechanism to load the DLL. Anytime the first remote desktop session is established…
An example of the potential malicious Registry Entry is shown below:
In a test scenario, I created a DLL that – when loaded – creates a c:\test\test_attached file.
The following screenshot shows what happens:
- The user is logged on (console session) – the two first commands show situation at that moment and no presence of the file created by the DLL
- The user then logs on remotely (under the same account – rdp-tcp#1 session).
- The moment user logs on, the c:\test\test_attached file is created – the code is loaded
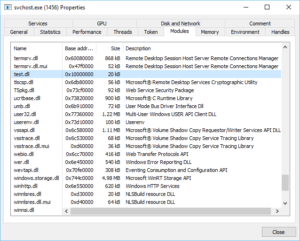
The c:\test\test.dll is loaded into svchost.exe process and stays resident (until reboot/service restart)