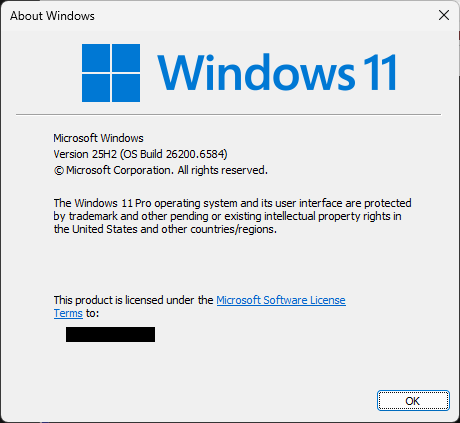
When you run winver it calls the shell32.dll!ShellAbout function to display the following dialog box:
It turns out the ShellAbout function’s declaration makes it a potential target for calling it from rundll32.exe, even if its prototype doesn’t follow the rundll32 calling protocol.
The function accepts the following parameters:
INT ShellAboutA( [in, optional] HWND hWnd, [in] LPCSTR szApp, [in, optional] LPCSTR szOtherStuff, [in, optional] HICON hIcon );
and the rundll32 callback is declared as:
RunDll32EntryPoint( HWND hwnd, HINSTANCE hinst, LPSTR lpszCmdLine, int nCmdShow );
In other words, the mapping of the function arguments looks like this:
HWND hWnd -> HWND hwnd LPCSTR szApp -> HINSTANCE hinst LPCSTR szOtherStuff -> lpszCmdLine HICON hIcon -> nCmdShow
So, by calling:
rundll32.exe shell32.dll, ShellAbout Visit http://extend-windows-license-by-10-years-for-free.com now!
we fill-in the following bit:
LPCSTR szOtherStuff -> lpszCmdLine
with a string provided via a command line.
And as the API documentation describes, this parameter is:
A pointer to a null-terminated string that contains text to be displayed in the dialog box after the version and copyright information. This parameter can be NULL.
Thanks to that coincidence, the result of our rundl32 invocation is the following dialog box:

If you paid attention, you probably noticed that the title of the dialog box got corrupted:

but that’s a side-effect of szApp parameter getting some random value from the stack/rdx register (if you follow the calling conventions of x86/x64).
Rest assured that this is not a security risk, but just yet another example of using Windows API in a slightly unorthodox way, similar to this example I posted about a few years back…